Following the revelation of four zero-day vulnerabilities currently affecting Microsoft Exchange server, Check Point Research (CPR) disclosed its latest observations on exploitation attempts against organisations that it tracks worldwide.
- CPR has seen thousands of exploit attempts against organisations worldwide.
- CPR has observed that the number of attempted attacks has increased tenfold from 700 on March 11 to over 7200 on March 15.
- The country most attacked has been the United States (17% of all exploit attempts), followed by Germany (6%), the United Kingdom (5%), the Netherlands (5%) and Russia (4%).
- The most targeted industry sectors have been government/military (23% of all exploit attempts), followed by manufacturing (15%), banking and financial services (14%), software vendors (7%) and healthcare (6%).
Since the recently disclosed vulnerabilities on Microsoft Exchange servers, a full race has started amongst hackers and security professionals. Global experts are using massive preventative efforts to combat hackers who are working day in and day out to produce an exploit that can successfully leverage the remote code execution vulnerabilities in Microsoft Exchange.
CPR has outlined the disclosed vulnerabilities, the targeted organisations by country and industry, and then recommendations to prevent the attacks, which are yet to come.
Current attack attempts in numbers
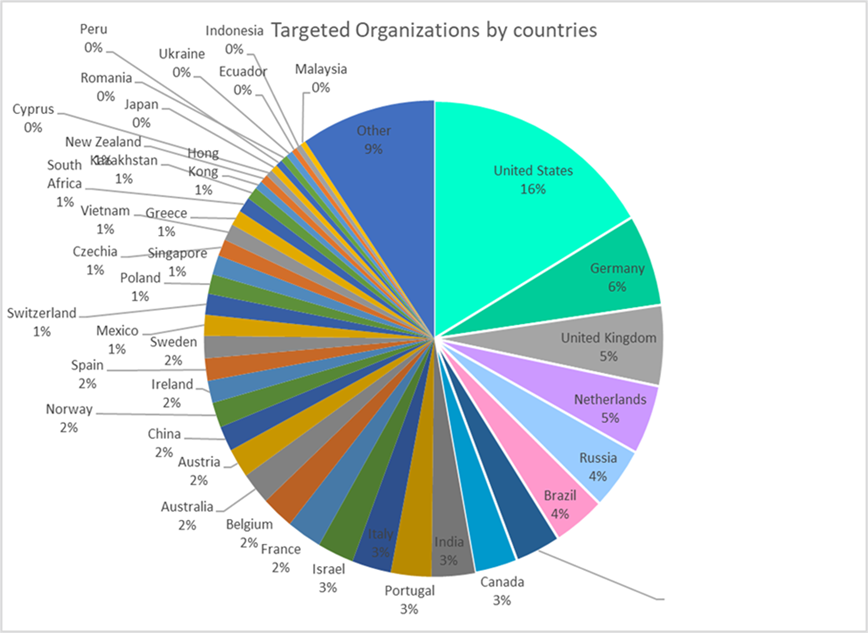
The country most attacked has been the United States (16 % of all exploit attempts), followed by Germany (6%), the United Kingdom (5%), the Netherlands (5%) and Russia (4%).
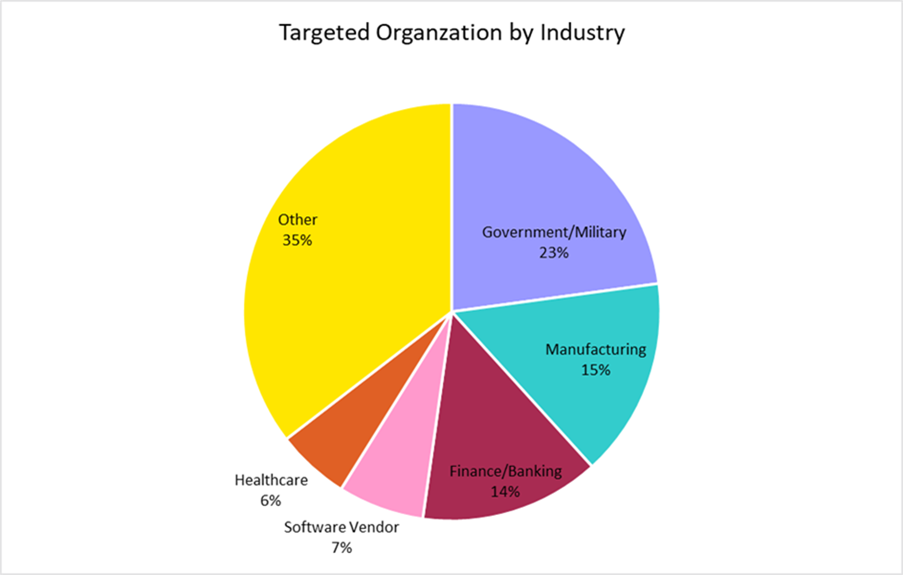
The most targeted industry sector has been government/military (23% of all exploit attempts), followed by manufacturing (15%), banking and financial services (14%), software vendors (7%) and healthcare (6%).
Behind-the-scenes of the zero days
On 3 March 2021, Microsoft released an emergency patch for its Exchange server product, the most popular mail server worldwide. All incoming and outgoing emails, calendar invitations and virtually anything accessed within Outlook goes through the Exchange server.
Orange Tsai (Cheng-Da Tsai) from DEVCORE, a security firm based in Taiwan, reported two vulnerabilities in January. Unaware of the full magnitude of these findings, Microsoft was prompted to further investigate its Exchange server. The investigation uncovered five more critical vulnerabilities which allow an attacker to read emails from an Exchange server without authentication or accessing an individual’s email account. Further vulnerability chaining enables attackers to completely take over the mail server itself.
Once an attacker takes over the Exchange server, he/she can open the network to the internet and access it remotely. Since many Exchange servers have internet exposer (specifically Outlook Web Access feature) and are integrated within the broader network, this poses a critical security risk for millions of organisations.
Yaniv Balmas, head of Cyber Research
Lotem Finkelsteen, head of Threat Intelligence
Adi Ikan, head of Network Research and Protection
Sagi Tzadik, Security Researcher